Search K
Appearance
Appearance
Other ways to support HackTricks:
A macOS installer package (also known as a .pkg file) is a file format used by macOS to distribute software. These files are like a box that contains everything a piece of software needs to install and run correctly.
The package file itself is an archive that holds a hierarchy of files and directories that will be installed on the target computer. It can also include scripts to perform tasks before and after the installation, like setting up configuration files or cleaning up old versions of the software.
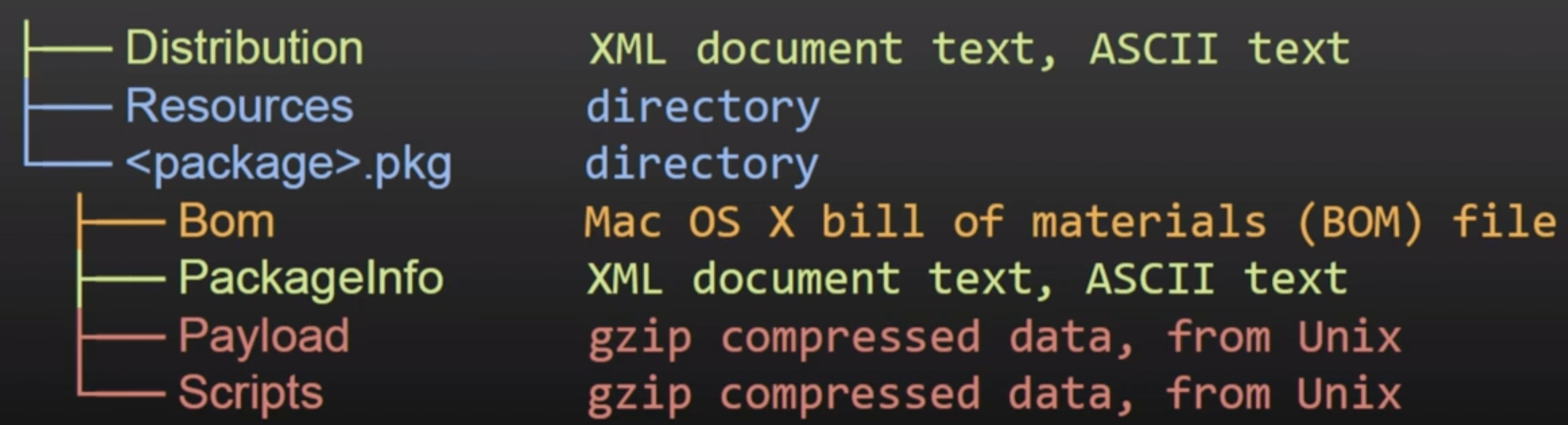
install-location from PackageInfo# Tool to directly get the files inside a package
pkgutil —expand "/path/to/package.pkg" "/path/to/out/dir"
# Get the files ina. more manual way
mkdir -p "/path/to/out/dir"
cd "/path/to/out/dir"
xar -xf "/path/to/package.pkg"
# Decompress also the CPIO gzip compressed ones
cat Scripts | gzip -dc | cpio -i
cpio -i < ScriptsIn order to visualize the contents of the installer without decompressing it manually you can also use the free tool Suspicious Package.
DMG files, or Apple Disk Images, are a file format used by Apple's macOS for disk images. A DMG file is essentially a mountable disk image (it contains its own filesystem) that contains raw block data typically compressed and sometimes encrypted. When you open a DMG file, macOS mounts it as if it were a physical disk, allowing you to access its contents.
❌
Note that .dmg installers support so many formats that in the past some of them containing vulnerabilities were abused to obtain kernel code execution.
.DTn2cEdQ.png)
The hierarchy of a DMG file can be different based on the content. However, for application DMGs, it usually follows this structure:
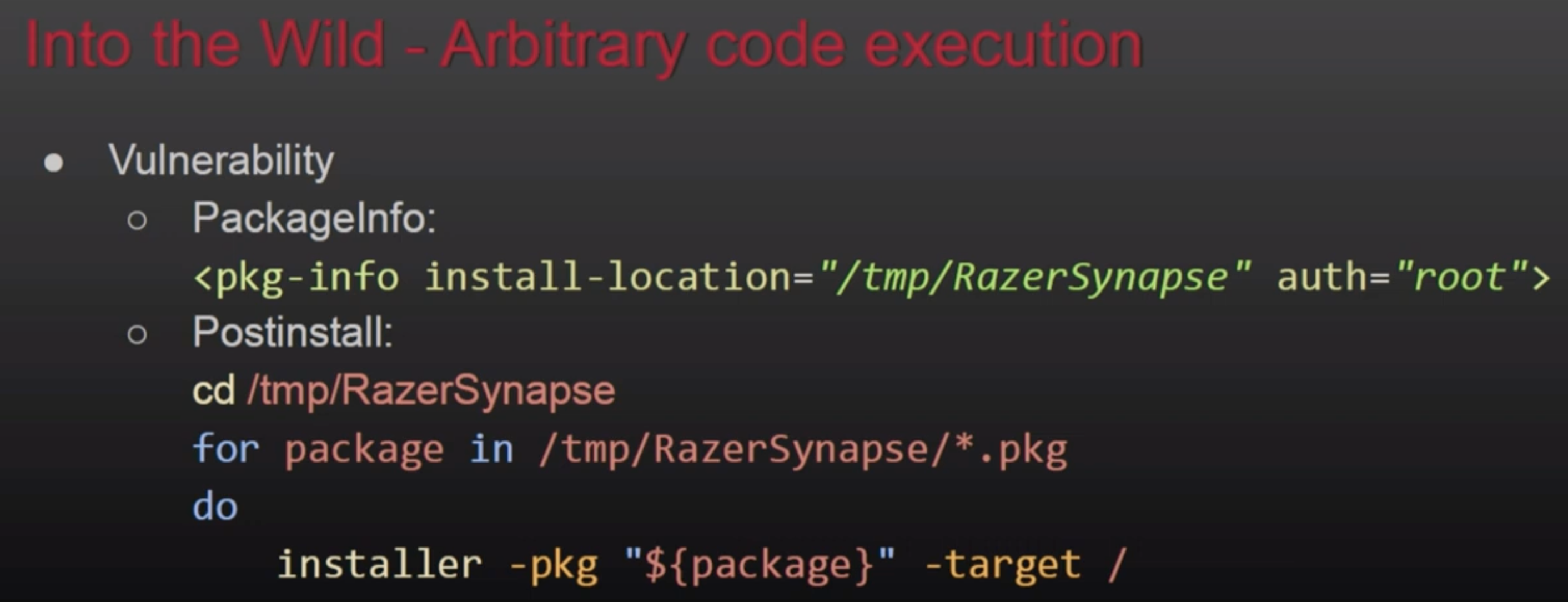
If a pre or post installation script is for example executing from /var/tmp/Installerutil, and attacker could control that script so he escalate privileges whenever it's executed. Or another similar example:
This is a public function that several installers and updaters will call to execute something as root. This function accepts the path of the file to execute as parameter, however, if an attacker could modify this file, he will be able to abuse its execution with root to escalate privileges.
# Breakpoint in the function to check wich file is loaded
(lldb) b AuthorizationExecuteWithPrivileges
# You could also check FS events to find this missconfigFor more info check this talk: https://www.youtube.com/watch?v=lTOItyjTTkw
If an installer writes to /tmp/fixedname/bla/bla, it's possible to create a mount over /tmp/fixedname with noowners so you could modify any file during the installation to abuse the installation process.
An example of this is CVE-2021-26089 which managed to overwrite a periodic script to get execution as root. For more information take a look to the talk: OBTS v4.0: "Mount(ain) of Bugs" - Csaba Fitzl
It's possible to just generate a .pkg file with pre and post-install scripts without any payload.
It's possible to add <script> tags in the distribution xml file of the package and that code will get executed and it can execute commands using system.run:
.Cl0j_cUA.png)
Other ways to support HackTricks: