Search K
Appearance
Appearance
.SFw_cIWc.png)
Use Trickest to easily build and automate workflows powered by the world's most advanced community tools.
Get Access Today:
Other ways to support HackTricks:
An Access Control List (ACL) consists of an ordered set of Access Control Entries (ACEs) that dictate the protections for an object and its properties. In essence, an ACL defines which actions by which security principals (users or groups) are permitted or denied on a given object.
There are two types of ACLs:
The process of accessing a file involves the system checking the object's security descriptor against the user's access token to determine if access should be granted and the extent of that access, based on the ACEs.
Each user session is associated with an access token that contains security information relevant to that session, including user, group identities, and privileges. This token also includes a logon SID that uniquely identifies the session.
The Local Security Authority (LSASS) processes access requests to objects by examining the DACL for ACEs that match the security principal attempting access. Access is immediately granted if no relevant ACEs are found. Otherwise, LSASS compares the ACEs against the security principal's SID in the access token to determine access eligibility.
There arey three main types of Access Control Entries (ACEs):
Each ACE has four critical components:
Access determination is conducted by sequentially examining each ACE until:
The way ACEs (rules that say who can or cannot access something) are put in a list called DACL is very important. This is because once the system gives or denies access based on these rules, it stops looking at the rest.
There is a best way to organize these ACEs, and it is called "canonical order." This method helps make sure everything works smoothly and fairly. Here is how it goes for systems like Windows 2000 and Windows Server 2003:
This setup helps in two big ways:
By doing things this way, the owner of a file or folder can be very precise about who gets access, making sure the right people can get in and the wrong ones can't.
So, this "canonical order" is all about making sure the access rules are clear and work well, putting specific rules first and organizing everything in a smart way.
.SFw_cIWc.png)
Use Trickest to easily build and automate workflows powered by the world's most advanced community tools.
Get Access Today:
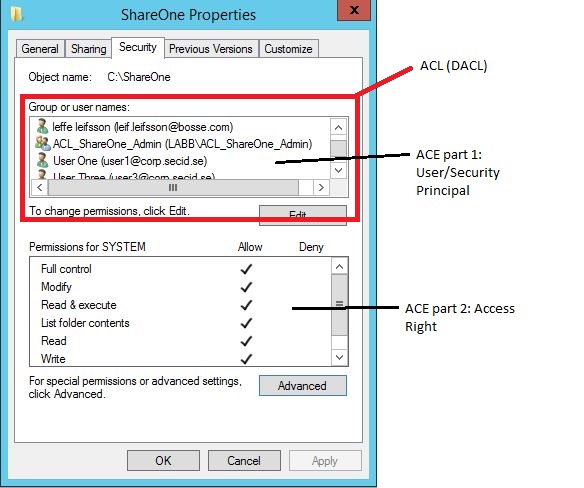
This is the classic security tab of a folder showing the ACL, DACL and ACEs:
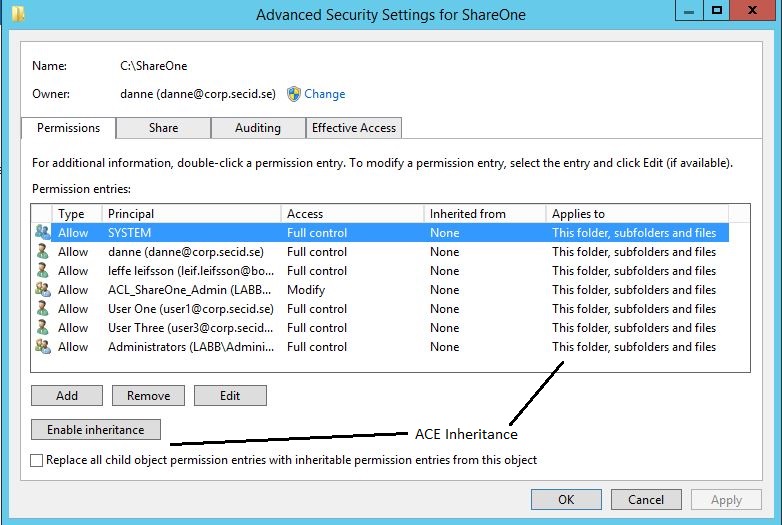
If we click the Advanced button we will get more options like inheritance:
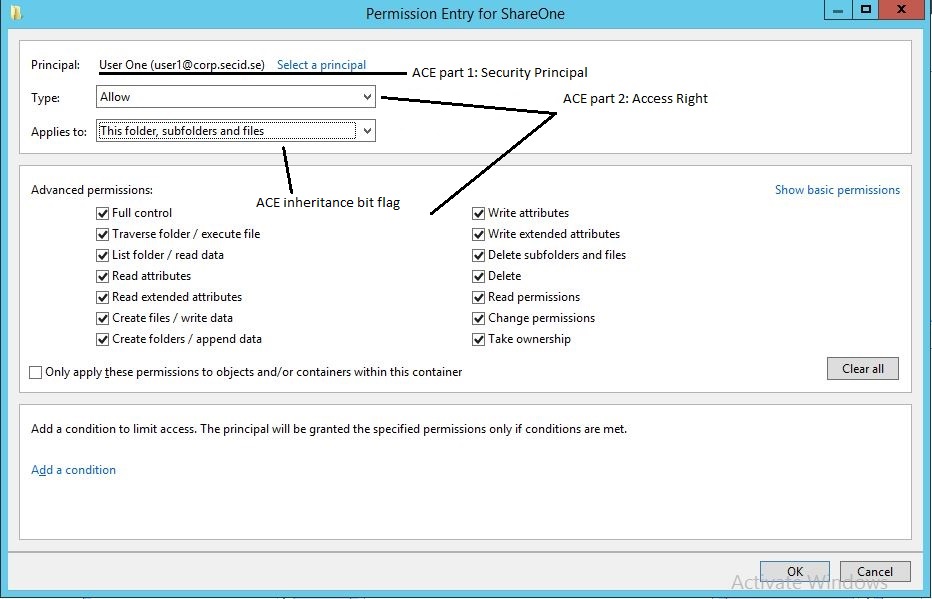
And if you add or edit a Security Principal:
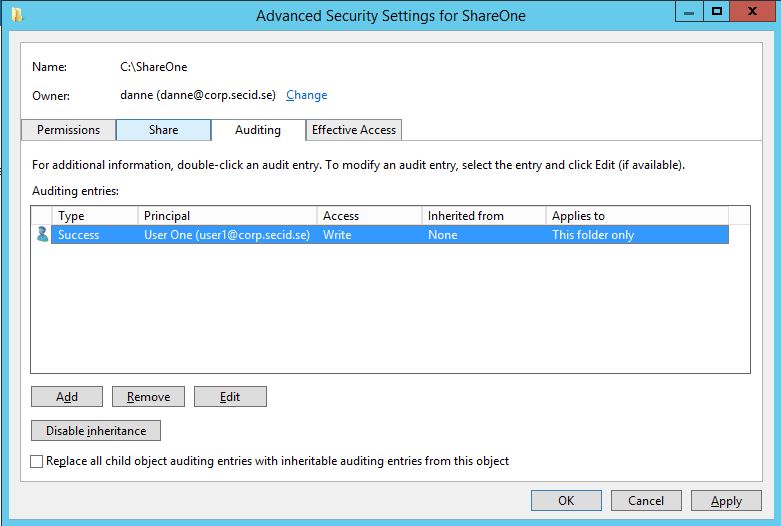
And last we have the SACL in the Auditing tab:
When managing access to resources, like a folder, we use lists and rules known as Access Control Lists (ACLs) and Access Control Entries (ACEs). These define who can or cannot access certain data.
Imagine you have a folder named Cost, and you want everyone to access it except for a marketing team. By setting up the rules correctly, we can ensure that the marketing team is explicitly denied access before allowing everyone else. This is done by placing the rule to deny access to the marketing team before the rule that allows access to everyone.
Let's say Bob, the marketing director, needs access to the Cost folder, even though the marketing team generally shouldn't have access. We can add a specific rule (ACE) for Bob that grants him access, and place it before the rule that denies access to the marketing team. This way, Bob gets access despite the general restriction on his team.
ACEs are the individual rules in an ACL. They identify users or groups, specify what access is allowed or denied, and determine how these rules apply to sub-items (inheritance). There are two main types of ACEs:
Each ACE contains important information like who the rule applies to (using a Security Identifier or SID), what the rule allows or denies (using an access mask), and how it's inherited by other objects.
In summary, ACLs and ACEs help define precise access controls, ensuring that only the right individuals or groups have access to sensitive information or resources, with the ability to tailor access rights down to the level of individual properties or object types.
| ACE Field | Description |
|---|---|
| Type | Flag that indicates the type of ACE. Windows 2000 and Windows Server 2003 support six types of ACE: Three generic ACE types that are attached to all securable objects. Three object-specific ACE types that can occur for Active Directory objects. |
| Flags | Set of bit flags that control inheritance and auditing. |
| Size | Number of bytes of memory that are allocated for the ACE. |
| Access mask | 32-bit value whose bits correspond to access rights for the object. Bits can be set either on or off, but the setting's meaning depends on the ACE type. For example, if the bit that corresponds to the right to read permissions is turned on, and the ACE type is Deny, the ACE denies the right to read the object's permissions. If the same bit is set on but the ACE type is Allow, the ACE grants the right to read the object's permissions. More details of the Access mask appear in the next table. |
| SID | Identifies a user or group whose access is controlled or monitored by this ACE. |
| Bit (Range) | Meaning | Description/Example |
|---|---|---|
| 0 - 15 | Object Specific Access Rights | Read data, Execute, Append data |
| 16 - 22 | Standard Access Rights | Delete, Write ACL, Write Owner |
| 23 | Can access security ACL | |
| 24 - 27 | Reserved | |
| 28 | Generic ALL (Read, Write, Execute) | Everything below |
| 29 | Generic Execute | All things necessary to execute a program |
| 30 | Generic Write | All things necessary to write to a file |
| 31 | Generic Read | All things necessary to read a file |
Other ways to support HackTricks:
.SFw_cIWc.png)
Use Trickest to easily build and automate workflows powered by the world's most advanced community tools.
Get Access Today: